External DNS with FreeIPA (RFC2136)¶
Sadly the External DNS Operator do not support RFC2136. Let's use the upstream one.
Thanks to astrid for the starting point.
Prepare IPA DNS Zone¶
Generate a TSIG key and register it¶
Configure the key at ipa server and all replicas¶
Allow DNS updates and zone transfer for the key¶
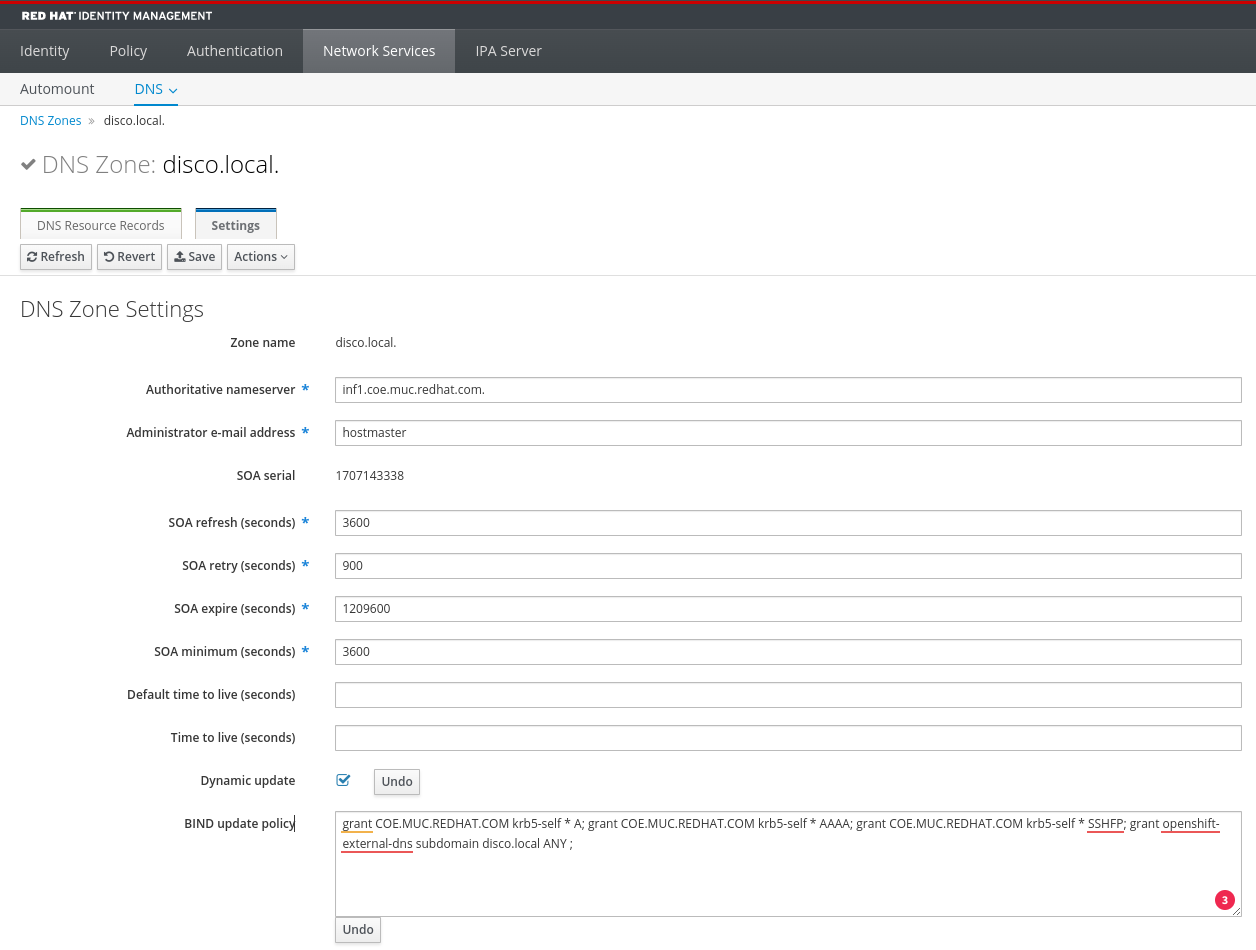
Select the zone you want to manage, in my example .disco.local:
- Enable
Dynamic update - Add
grant openshift-external-dns subdomain disco.local ANY ;to BIND update policy Details about the policy configuration you can here
-
Configure
Allow transferis not possible via WebUI. Becauseldap search example
At the ipa server
Deploy External DNS¶
based on Configuring RFC2136 provider
Deployment
Create a secret with the tsig key c3LyD11u....xX6WA==
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 | |
Check the logs of the external-dns pod
Example deployment¶
- Required MetalLB or support of service type LoadBalancer.